Edius Project Dongle Locker And Unlocker Today
Secure, scalable, and game-changing authentication for your applications. Get started in minutes with our powerful APIs and SDKs.

Secure, scalable, and game-changing authentication for your applications. Get started in minutes with our powerful APIs and SDKs.

Integrate into any programming language

A comprehensive suite of integrated tools for authentication, monetization, and user engagement.
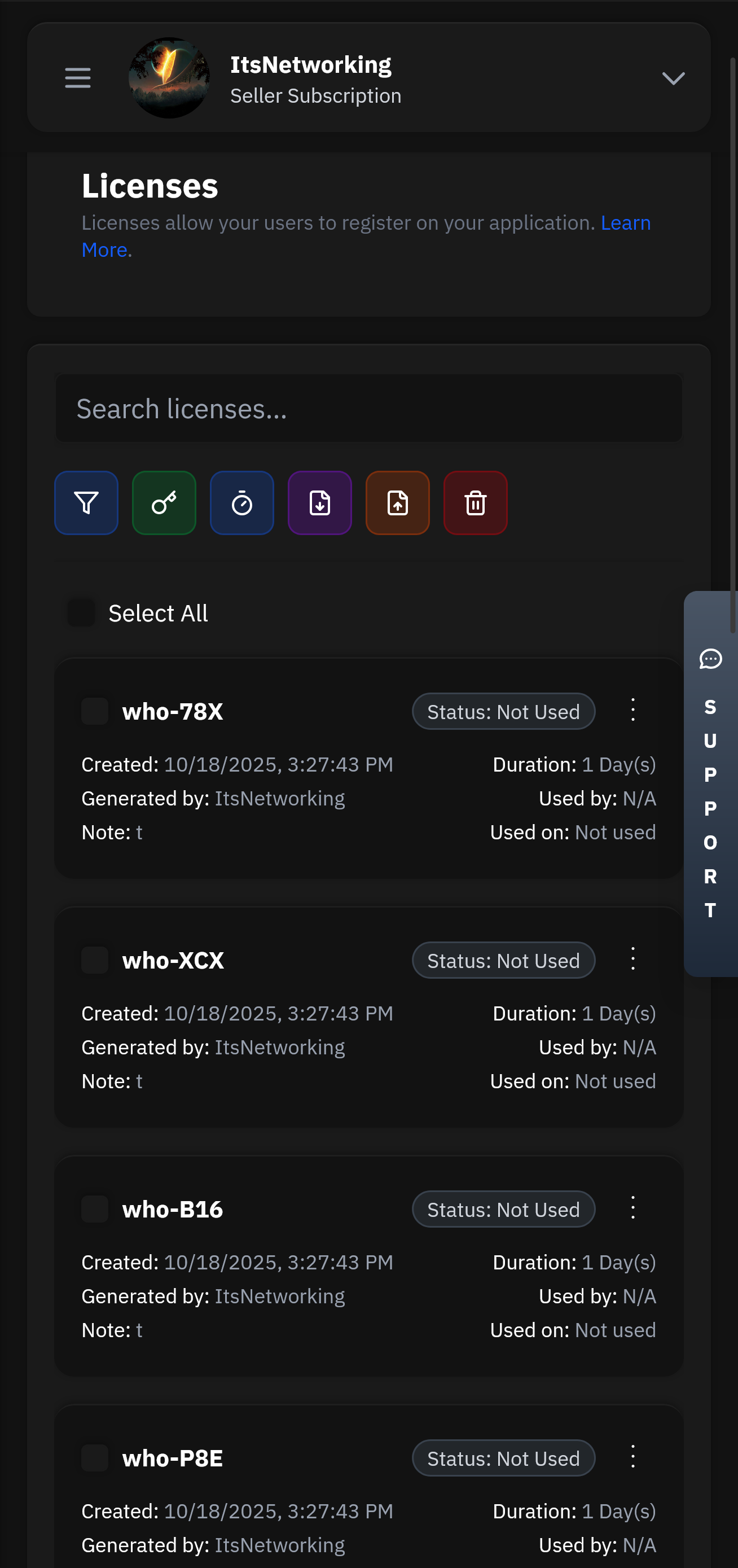
Create and manage user licenses with flexible expiration, trial, and subscription options.
Our lightning-fast infrastructure ensures your authentication requests are processed in under 50ms globally. With 99.99% uptime and redundant systems, your users will never experience delays.
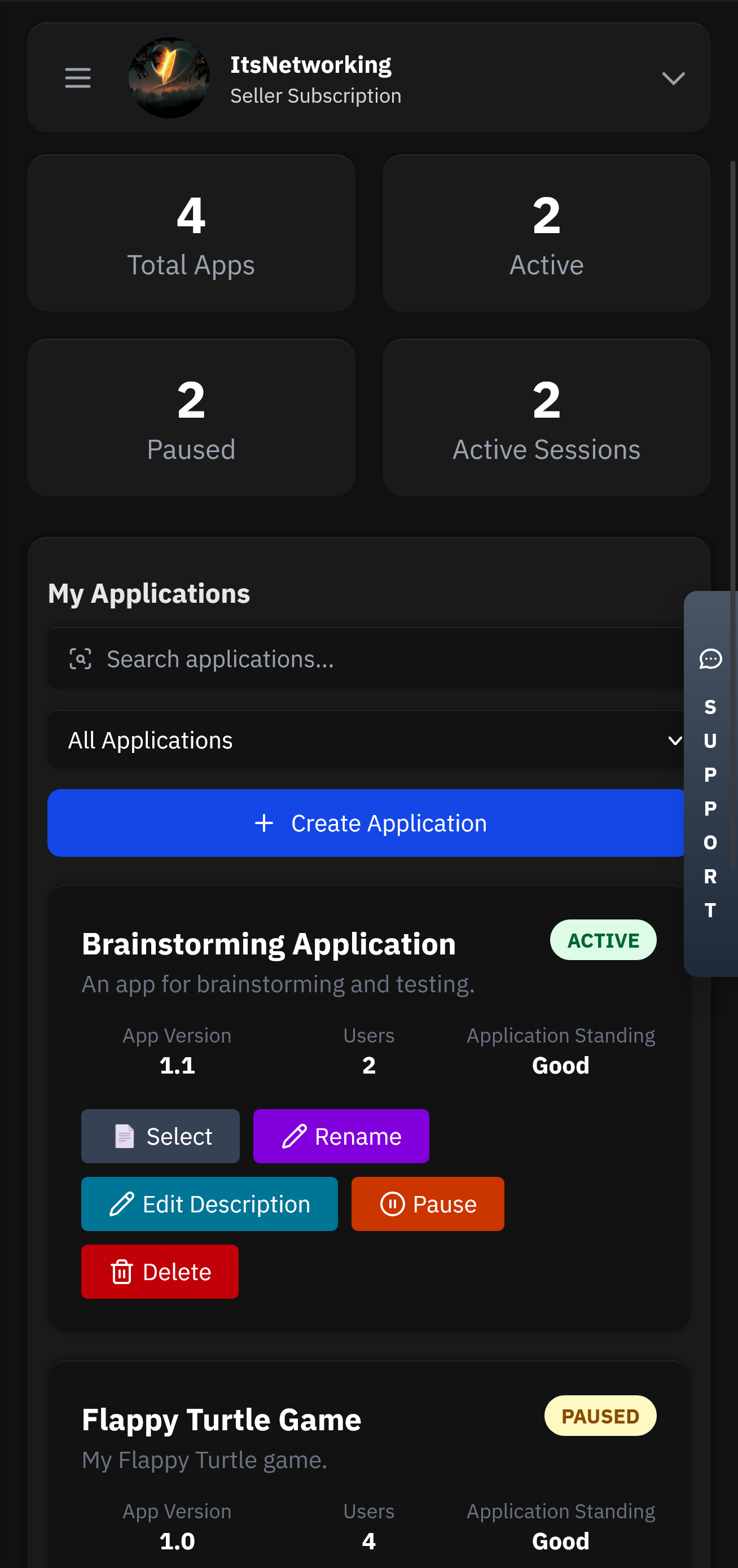
Manage your applications remotely with our powerful Seller API. Update licenses, ban users, modify subscriptions, and monitor usage from anywhere in the world with full administrative control.
Note: Some third-party "unlocker" tools claim to bypass these locks without the original dongle. Users should exercise extreme caution with such software, as it often violates licensing agreements and may contain security risks. Why Professionals Use Dongle Protection
To protect proprietary training materials and project templates used in video editing courses.
The term "unlocker" in this context refers to the software interface or "launcher" that decrypts the files in real-time for authorized users. When the correct dongle is present, the unlocker application acts as a bridge, allowing EDIUS to read the protected data as if it were a standard, unencrypted file.
Building a launcher application that the end-user will use to access the project once they have the authorized hardware key.
A project dongle locker is a security system that combines a physical hardware key (the dongle) with encryption software. It allows creators to "lock" their EDIUS project files (such as .ezp or .ezb extensions), making them accessible only when the specific, authorized hardware dongle is plugged into the computer.
Using a "Master Dongle" to run the encryption utility on your source folder.
Enables the safe sharing of projects; even if files are copied or emailed, they remain encrypted and useless without the physical key.
There's no question as to why we are the best choice for your business and one of the most used Authentication services.
Head over to our register page to create your account.
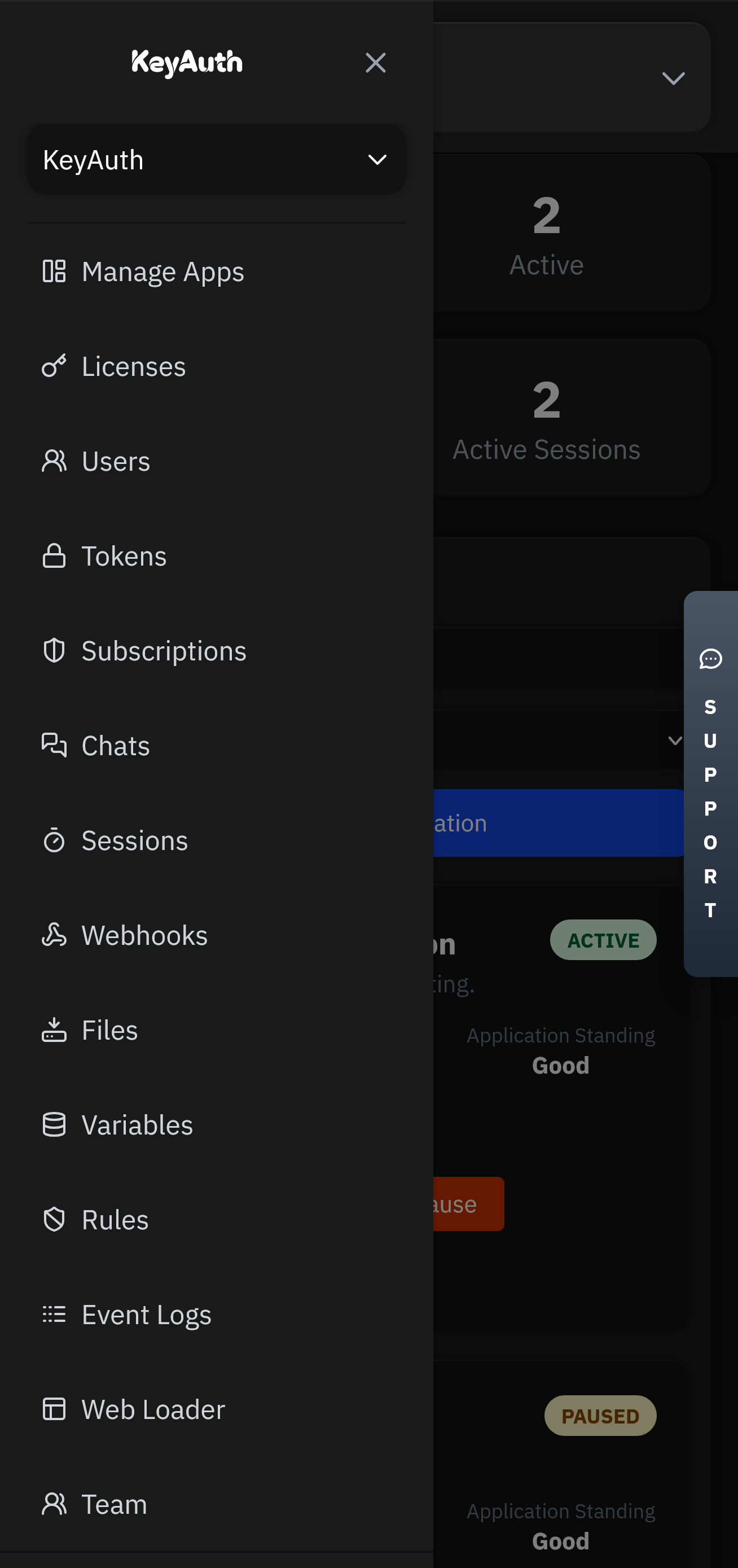
Applications will be the heart of your service. This is where all your users, licenses, chats and more will be stored.
Head over to our GitHub to find our examples and client API files. Simply follow the steps and have authentication up in less than 5 minutes.
Control your application from anywhere using our mobile app. Manage licenses, chat with users, and view analytics directly from your phone or tablet.
Flexible options for teams of all sizes.
Pick an attack, watch the defense, and estimate monthly revenue saved.
Note: Some third-party "unlocker" tools claim to bypass these locks without the original dongle. Users should exercise extreme caution with such software, as it often violates licensing agreements and may contain security risks. Why Professionals Use Dongle Protection
To protect proprietary training materials and project templates used in video editing courses. edius project dongle locker and unlocker
The term "unlocker" in this context refers to the software interface or "launcher" that decrypts the files in real-time for authorized users. When the correct dongle is present, the unlocker application acts as a bridge, allowing EDIUS to read the protected data as if it were a standard, unencrypted file.
Building a launcher application that the end-user will use to access the project once they have the authorized hardware key. Note: Some third-party "unlocker" tools claim to bypass
A project dongle locker is a security system that combines a physical hardware key (the dongle) with encryption software. It allows creators to "lock" their EDIUS project files (such as .ezp or .ezb extensions), making them accessible only when the specific, authorized hardware dongle is plugged into the computer.
Using a "Master Dongle" to run the encryption utility on your source folder. The term "unlocker" in this context refers to
Enables the safe sharing of projects; even if files are copied or emailed, they remain encrypted and useless without the physical key.



Got questions? We've got answers. If you can't find what you're looking for, feel free to reach out to our support team.